Guide to Implementing SPIFFE for Autonomous AI Agents
Overview
As artificial intelligence systems become increasingly autonomous and agentic, ensuring their identity and trustworthiness becomes a critical challenge. Traditional identity frameworks built around human users and static credentials fall short when applied to dynamic, ephemeral, and non-human entities. SPIFFE (Secure Production Identity Framework For Everyone) is a battle-tested open standard that addresses this challenge by providing a secure identity framework for workloads. Originally developed for microservices in cloud-native environments, SPIFFE issues and validates cryptographically verifiable identities without relying on long-lived secrets like passwords or API keys. This tutorial will guide you through the process of implementing SPIFFE for autonomous AI agents, enabling them to prove their identity, establish trust, and communicate securely within multi-agent systems.
Prerequisites
- Basic understanding of TLS and mutual TLS (mTLS)
- Familiarity with containerization (Docker, Kubernetes)
- Knowledge of SPIRE (SPIFFE Runtime Environment) – the reference implementation
- Access to a Linux environment with root or sudo privileges
- Go runtime (v1.20+) or ability to run prebuilt SPIRE binaries
- Network connectivity between SPIRE server and agents
Step-by-Step Implementation
1. Install SPIRE Server and Agent
Download the latest SPIRE release from the official GitHub page. Extract the tarball and navigate to the SPIRE directory.
wget https://github.com/spiffe/spire/releases/download/v1.9.4/spire-1.9.4-linux-x86_64.tar.gz
tar -xzf spire-1.9.4-linux-x86_64.tar.gz
cd spire-1.9.4Start the SPIRE server with a minimal configuration file (server.conf):
./bin/spire-server run -config conf/server/server.confSimilarly, start the SPIRE agent on each node where AI agents run. The agent configuration file (agent.conf) must point to the server address and trust bundle.
2. Configure Trust Domain and Registration
Define a trust domain, e.g., example.org. This becomes the namespace for all SPIFFE IDs. Use the server CLI to create a registration entry for an AI agent workload:
./bin/spire-server entry create \
-spiffeID spiffe://example.org/ai-agent/agent-01 \
-selector unix:uid:1001 \
-parentID spiffe://example.org/spire/agent/join_tokenThe selector identifies the workload (e.g., Unix user ID). Replace uid:1001 with the actual UID of your AI agent process.
3. Issue SPIFFE IDs for AI Agents
Once the agent is registered, the SPIRE agent on the node automatically picks up the entry and issues a X.509 SVID (SPIFFE Verifiable Identity Document) to the workload. The AI agent can obtain its SVID by calling the SPIRE agent’s Workload API. For example, using the SPIRE agent’s gRPC stream:
# Typical code snippet in Go for an AI agent
import (
"context"
"github.com/spiffe/go-spiffe/v2/workloadapi"
)
// Create a Workload API client
client, err := workloadapi.New(context.Background())
if err != nil { panic(err) }
// Fetch the SVID
svid, err := client.FetchX509SVID(context.Background())
if err != nil { panic(err) }
// Use svid.Certificates for mTLSFor other languages (Python, Java), similar libraries exist.
4. Enable mTLS Between AI Agents
With SVIDs in hand, configure AI agents to perform mutual TLS. Each agent presents its certificate (SVID) and validates the peer’s certificate against the trust bundle. Example using Go:
tlsConfig := &tls.Config{
GetClientCertificate: func(info *tls.CertificateRequestInfo) (*tls.Certificate, error) {
return &tls.Certificate{Certificate: svid.Certificates, PrivateKey: svid.PrivateKey}, nil
},
InsecureSkipVerify: false,
VerifyPeerCertificate: func(rawCerts [][]byte, verifiedChains [][]*x509.Certificate) error {
// Custom validation using SPIRE trust bundle
return nil
},
}Now AI agents can authenticate each other using SPIFFE identities, ensuring every interaction is encrypted and verified.
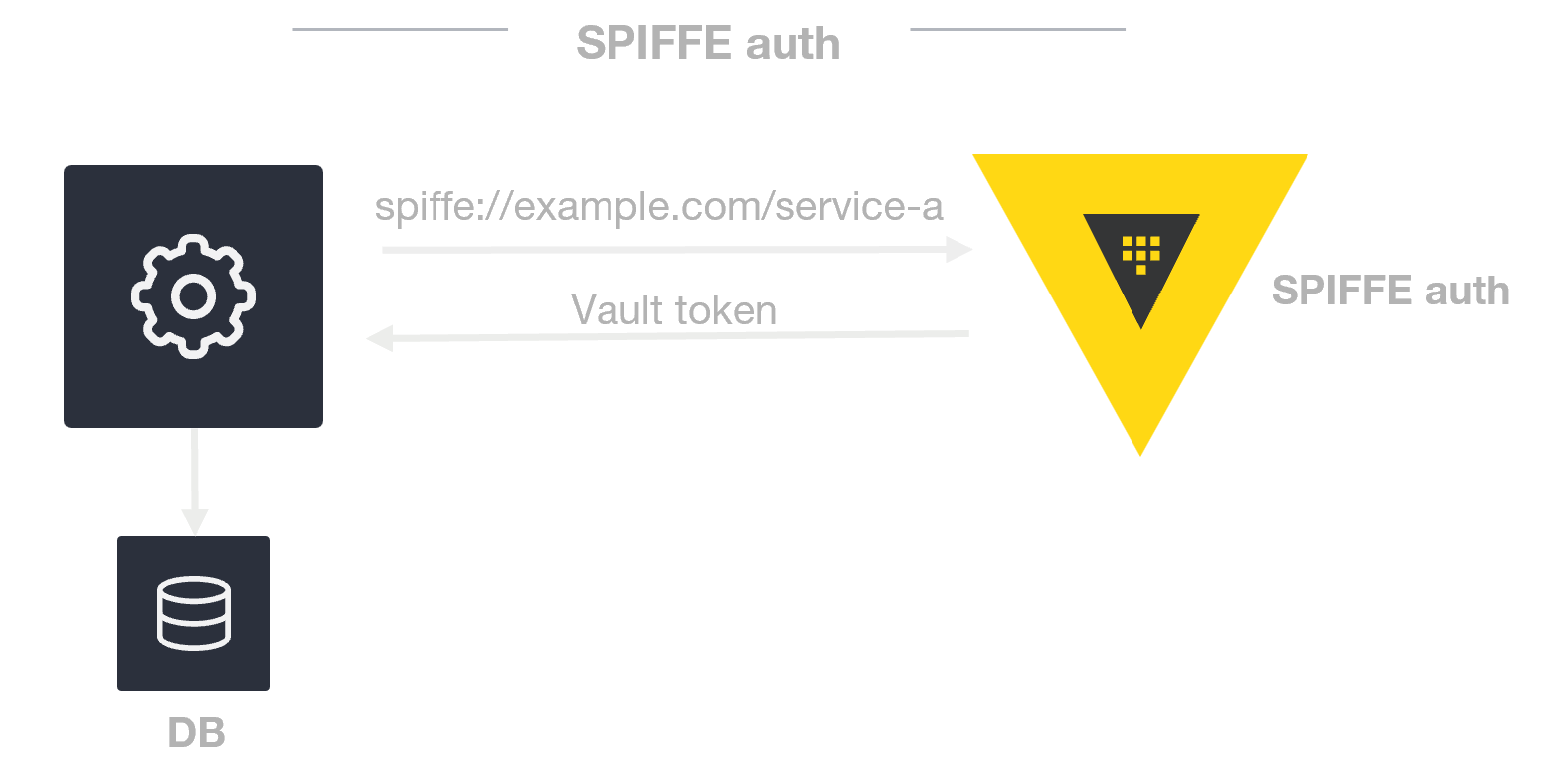
5. Federation Across Trust Domains
For multi-agent systems spanning multiple organizations or clouds, configure federation between SPIFFE trust domains. Each SPIRE server exposes a federation endpoint. Export trust bundles from Domain A and import into Domain B.
# On Domain A server:
./bin/spire-server bundle show > domain-a-bundle.pem
# On Domain B server:
./bin/spire-server bundle set -id spiffe://domain-a.org -path domain-a-bundle.pemAfter federation, an AI agent from Domain A can authenticate with an agent in Domain B using their respective SPIFFE IDs.
Common Mistakes
- Misconfigured trust domain: Using inconsistent trust domain names across server and agents leads to authentication failures. Always verify the domain matches in all configuration files.
- Not rotating keys: SVIDs have a finite lifetime. If the SPIRE agent fails to rotate them automatically (e.g., due to clock skew), workloads lose valid credentials. Ensure NTP is synchronized.
- Ignoring revocation: A compromised AI agent should have its SPIFFE ID revoked immediately. Use the SPIRE server’s
entry deleteorbancommand, but many tutorials skip this step. - Selector mismatch: The selector (e.g., Unix UID) must exactly match the running workload’s attributes. Using the wrong PID or path results in no SVID being issued.
- Overly permissive registration entries: Avoid wildcard selectors; always use specific selectors to limit which processes get SPIFFE IDs.
Summary
SPIFFE provides a robust, open-standard identity framework for autonomous AI agents and other non-human actors. By following this guide, you have learned how to install SPIRE, configure trust domains, issue dynamic identities, enable mTLS, and federate across domains. Implementing SPIFFE ensures verifiable workload identity, supports zero-trust architectures, and enables secure collaboration in multi-agent environments. With proper lifecycle management and attention to common pitfalls, SPIFFE becomes an essential component for production-grade agentic AI systems.
Related Articles
- Navigating the PC Upgrade Dilemma: A Step-by-Step Guide to Cost-Effective Building in 2026
- Framework Laptop 13 Pro: Everything You Need to Know About the Upgraded Modular Powerhouse
- Home Data Centers: Can Your House Power the Next AI Revolution?
- Breakthrough Coherent Raman Method Enables Direct Detection of Ultrathin Molecular Layers at Interfaces
- 7 Ways Tanzu Platform's 15-Year Head Start Prepares You for the AI Revolution
- 10 Surprising Features of Lian Li's DK07 Wood Motorized Standing Desk That Doubles as a PC Case
- A Practical Guide to the Rowhammer Attack on NVIDIA Ampere GPUs
- How to Save Big on Samsung Galaxy and Amazon Echo Displays: A Step-by-Step Guide